Penetration testing tutorials
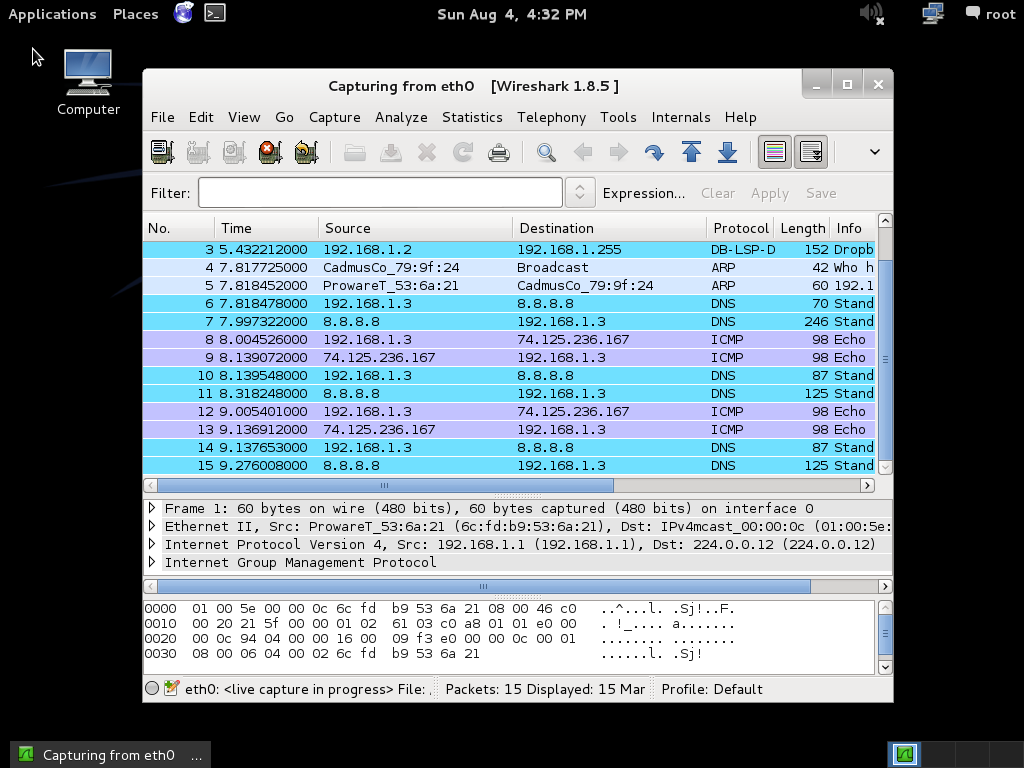
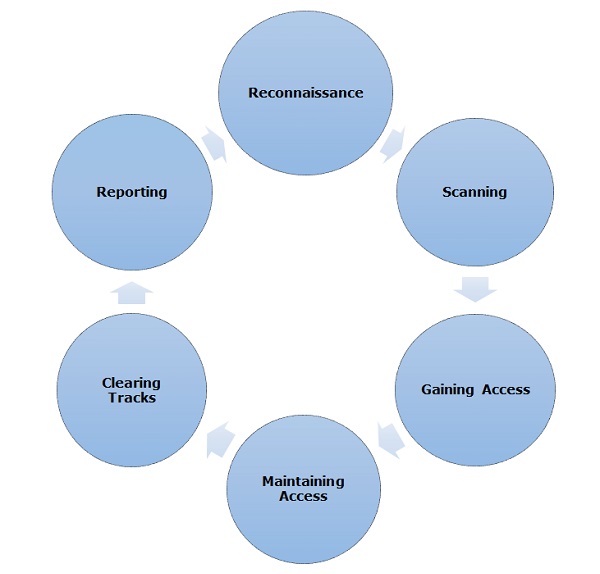
What is penetration testing? Exploits often deliver a payload to the target system to grant the attacker access to the system. In this module we will know how to penetrate wireless networks, break wireless keys and analyze captured packets for juicy information. We will discover how can we carry out another type of testing but against connected clients, so be ready to discover the wireless client side attacks. Penetration testing requires that you get permission from the person who owns the system. If you are not a subscriber and want to buy this magazine click here. For example, you can upload and download files from the system, take screenshots, and collect password hashes.


Programming and Testing Tutorials for Beginners - TechBeamers


Penetration testing tutorial: Guidance for effective pen tests
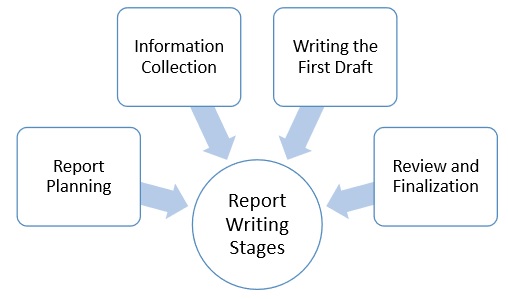
Penetration testing requires that you get permission from the person who owns the system. Pen test tools Many security solution providers perform a wide variety of penetration tests for their customers. Penetration testing is an essential feature that needs to be performed regularly for securing the functioning of a system. Azure Cosmos DB flexes joints for multiple data stores Microsoft added multi-master write replication and more granular cost controls to Cosmos DB to cover the broadest number of uses Verizon has built a software-defined networking controller for its legacy routers.

Best Windows Penetration testing tools :
The vendor's UK channel chief is encouraging partners to add their own 'secret sauce' to its cloud portfolio. The evolution of network access control Networking blogs: Number of Slack users soars, but Enterprise Grid adoption unclear More than 8 million people use Slack every day, and 3 million people are paid subscribers. Verizon SDN used to manage legacy Cisco, Juniper routers Verizon has built a software-defined networking controller for its legacy routers.



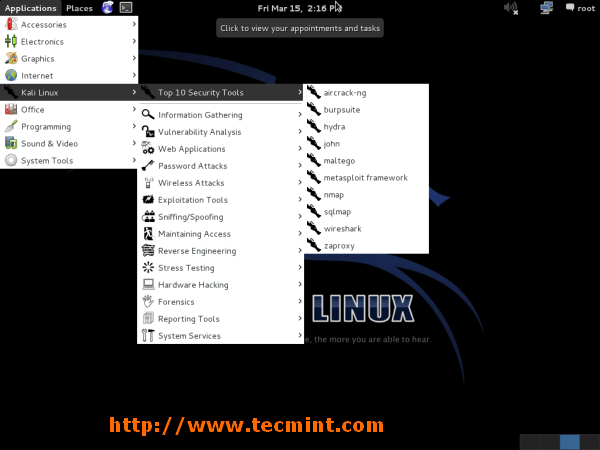
It still is the best payload. Be the First to Comment! Hello everyone, i would have made the biggest mistake of my life marrying my former spouse but before the marriage after i saw his link from someones else testimonial. Evil Twin Attack Cheating your way into hacking that third wifi again - Fluxion: This guide is intended to be educational as well as entertaining. A vulnerability is a security hole in a piece of software, hardware or operating system that provides a potential angle to attack the system. This guide will teach you how to install Metasploit Framework in Ubuntu
907
58
















Stunning amateur Indian cutie with big boobs on webcam
tres jolis tour cela
NICE PUSSY
wow,,,,, i dream it
I love watching stroking hard cock watch you cum.
Now shes a good suckutary
jacking off on a girls back is a far cry from cumming in her mouth
que delicia